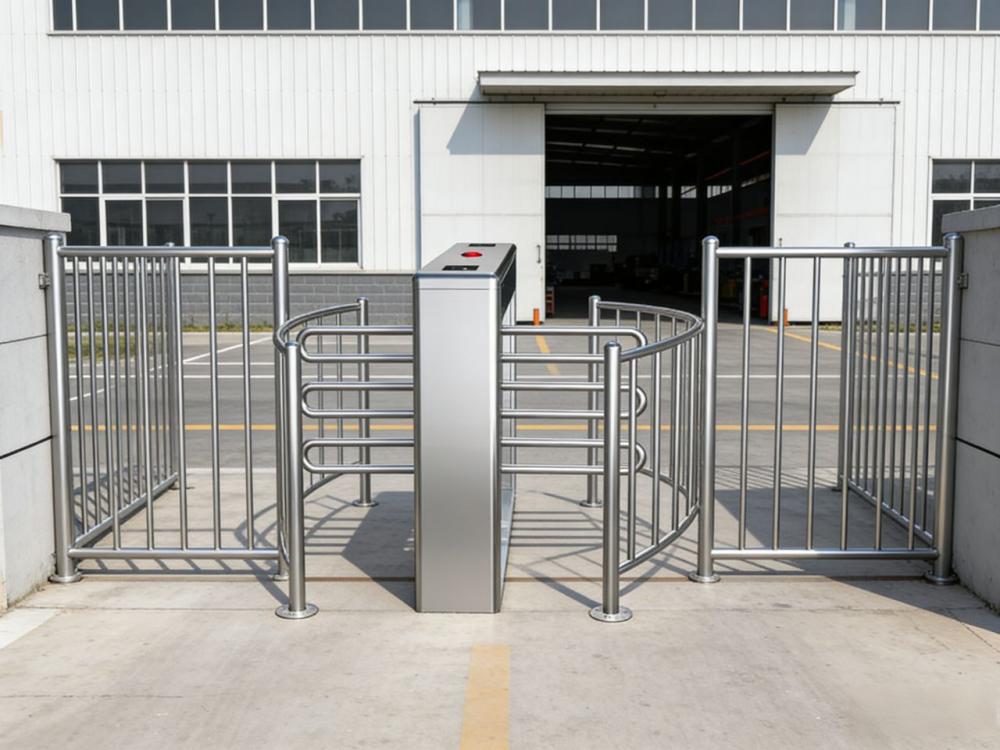
How Turnstile Access Control Systems Work ?
Turnstiles are devices designed to automate access control and pedestrian flow at entry and exit points. They not only conserve space and reduce labor costs but also efficiently manage high-volume pedestrian traffic. Turnstiles are particularly practical—and ubiquitous—in settings such as gyms, recreational facilities, commercial office buildings, and government institutions.

What is a Turnstile?
A turnstile is a specialized type of gate or barrier designed to allow only one person to pass through at a time. It serves as a tool for regulating the flow of people entering restricted areas or buildings. Some turnstiles operate under manual control, requiring staff members to manually trigger the unlocking mechanism to admit each individual passerby. For instance, at a sports stadium, staff members might admit spectators one by one after they present a valid ticket.
Other turnstiles are automated. These devices typically remain in a locked state, unlocking to grant passage only when an individual presents valid credentials. Various methods are employed to verify personal identity and authorize entry, including card scanning, fingerprint or facial recognition systems, and the entry of passcodes. Once the system recognizes valid access credentials, the turnstile automatically unlocks, allowing the individual to pass through unimpeded.
Types of turnstiles
Turnstile is an umbrella term for a range of different types of pedestrian barriers. Generally, turnstiles consist of a revolving set of barriers installed at a height to impede access.
Full-height turnstiles offer an added layer of security. Where waist-height turnstiles could be jumped over or crawled under, full-height turnstiles are more robust. They often consist of a series of horizontal bars from foot- to head-height forming a barrier. A series of these barriers revolve around a central point, with enough space between them to only allow one person to pass at a time.
Waist-height turnstiles are very common. They generally involve a set of horizontal barriers fixed on one side. The barrier could be a revolving tripod or an arm that rises or slides out of the way to allow access.
Biometric-Based Turnstile Access Control Systems
Biometric technology adds an extra layer of security to turnstile access control systems. Biometric solutions inherently offer several unique advantages. For instance, users must be physically present on-site to interact with the biometric reading device. In contrast, access cards can be lost or stolen, while keypad passcodes may be forgotten or compromised. To verify identity via fingerprints, iris patterns, or facial features, the user must be physically present in person.
Fingerprint Readers
Fingerprint readers integrate seamlessly with turnstiles to create highly efficient and practical access control systems. Users typically require no prior training to operate the fingerprint reader with ease. They are freed from the need to constantly remember to carry access cards or key fobs, as well as the burden of memorizing keypad passcodes. This advantage is particularly pronounced in settings such as gyms and leisure centers, where individuals often prefer not to carry extra items with them. High-performance fingerprint readers, utilizing multispectral imaging sensor technology, are capable of effective scanning and recognition even when moisture is present on the surface of the finger.
Facial Recognition Technology
To further enhance convenience, the turnstile system can also be integrated with facial recognition terminals. Facial recognition technology offers extremely rapid response speeds and remarkably simple operation—users need not carry any physical items, memorize any information, or even perform any additional actions. They simply need to look directly into the terminal's camera; once the system successfully identifies their facial features, it immediately grants them access. In busy, high-traffic environments, facial recognition technology stands as the ideal solution for avoiding queues and congestion while ensuring efficient passage through the turnstiles.
Card Readers and QR Codes for Turnstiles
Card readers are typically used in conjunction with traditional access cards, proximity key fobs, or tags, and are designed to verify the identity of individuals attempting to enter a secured area. Typically, card readers are mounted on the top or directly on the front face of the turnstile's side unit. As an individual approaches, they simply hold their access card or credential tag in close proximity to the reader. The unique identification data contained within the credential is then transmitted wirelessly to the reader.

In the case of a standalone access control system, the user database is stored internally within the card reader, which then directly determines whether to grant or deny access. In a networked access control system, the card reader transmits the relevant information to a central database; the user's access permission levels and other pertinent details are stored at this central location.
If the credential holder is verified as having authorized access to the area, the turnstile immediately unlocks. The individual may then push open the barrier arms to enter the area. After a preset period of time—or once the turnstile has completed a full rotation cycle—it automatically relocks, ready to await the next passing individual.
This constitutes an intelligent access system that integrates QR code recognition with access control functionality. Its operational workflow primarily comprises four steps: QR code generation, scanning and recognition, permission verification, and access control execution. First, the system generates an encrypted QR code for the user (which may be a dynamic code, a static code, or a temporary visitor code). The user then scans this code at the turnstile using a dedicated reader; the device decodes the QR code information and transmits it to a controller or backend system. Subsequently, the system verifies the validity, access permissions, and authorized time window of the QR code (this verification can be performed either online or locally offline). Upon successful verification, the controller issues a command to actuate the turnstile or door lock, thereby granting access. If verification fails, access is denied and an alert regarding the anomaly is triggered; concurrently, the system records all access data to facilitate subsequent management and auditing.